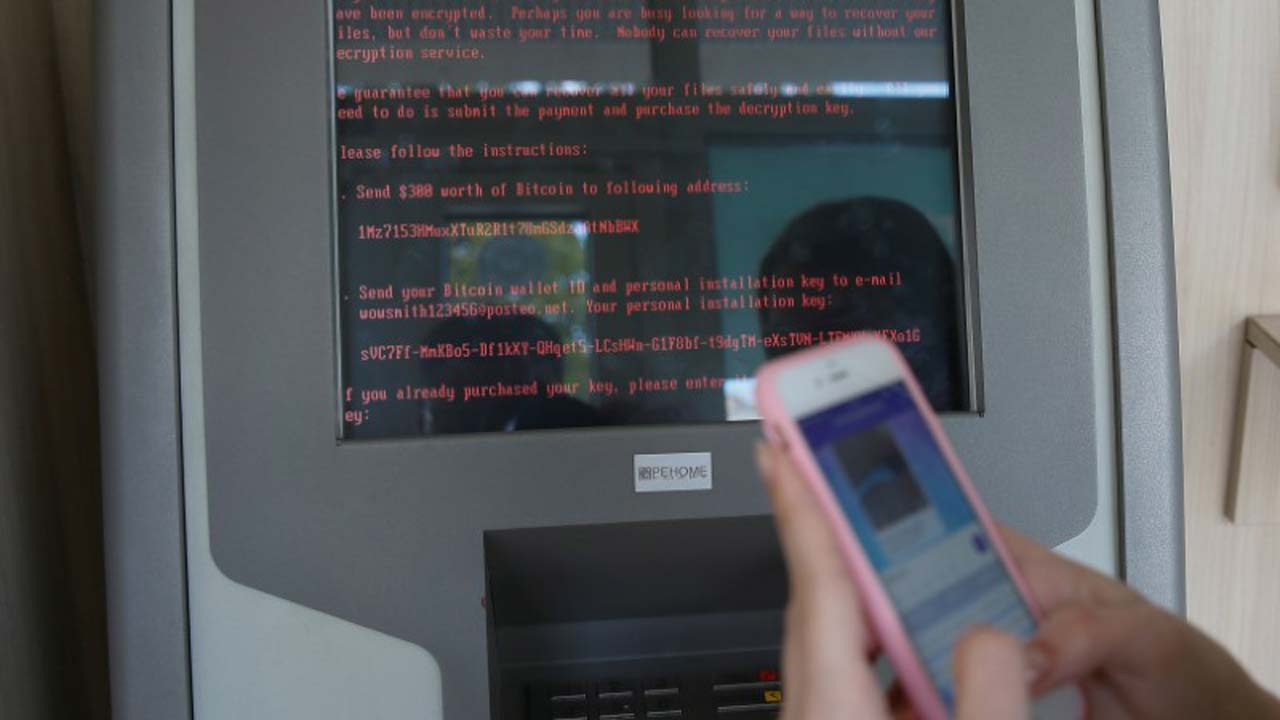
National Information Technology Development Agency (NITDA) and other cyber security firms have alerted Nigerian companies on the rampaging ransomware attacks called Petya or ‘GoldenEye’.
The deadly cyber-attack, similar to the recent ‘WannaCry’ attack, not only encrypts files but also encrypts hard drives, rendering entire computer system inaccessible.
Dr Isa Ali Pantami, director general/CEO of NITDA, said the attack has paralysed businesses across the world and is spreading quickly with reports indicating that countries affected so far include Ukraine, Denmark, Russia, the UK, Germany, France, Italy, Poland and the USA.
The malware is spreading using a vulnerability in Microsoft Windows that was patched in March 2017 — the same bug that was exploited by the WannaCry ransomware.
“While our CERRT team are working round the clock along with other stakeholders to come up with effective defence mechanism for the Nigerian cyberspace, we are calling on Network Administrators in the public and private sectors as well as individuals to take the following measures recommended during the recent WannaCry attack: isolate the system from your network to prevent the threat from further spreading; remove the system from Network; and do not use flash/pen drive, external drives on the System to copy files to other systems”, the DG said.
As a general precautionary measure, Dr. Pantami urged organisations, especially Government Agencies to regularly update their operating systems with the latest patches; regularly update their software applications with latest patches; turnoff unnecessary/unneeded features; avoid downloading and opening unsolicited files and attachments; adjust security software to scan compressed or archived files; and avoid indiscriminate use wireless connections, such as Bluetooth or infrared ports.
Olufemi Ake, country manager, Nigeria and Ghana, ESET, told Nigeria CommunicationsWeek the ransomware appears to specifically targeted at bringing down business IT systems.
“The outage began in Ukraine as the country’s power grid, airport, national bank and communications firms were first to report problems, before it spread rapidly throughout Europe.
“If you have a default install of any modern ESET product, ESET would protect against this threat. Additionally, any ESET product with network detection would protect from the SMB spreading mechanism – EternalBlue proactively.
Jitendra Bulani, PR manager, Emerging Markets at Sophos said in an email to Nigeria CommunicationsWeek that the new variant is particularly virulent because it uses multiple techniques to spread automatically within a company’s network once the first computer is infected.
“Sophos customers with Sophos Endpoint Protection products are protected against this new variant. Sophos Intercept X customers were proactively protected with no data encrypted, from the moment this new ransomware variant appeared.”
 Follow Us on Google News
Follow Us on Google News
 Follow Us on Google Discover
Follow Us on Google Discover